We are proud to announce that, iSystems has been awarded a "Caring Company" accredited by the Hong Kong Council of Social Service caring company again in 2019.
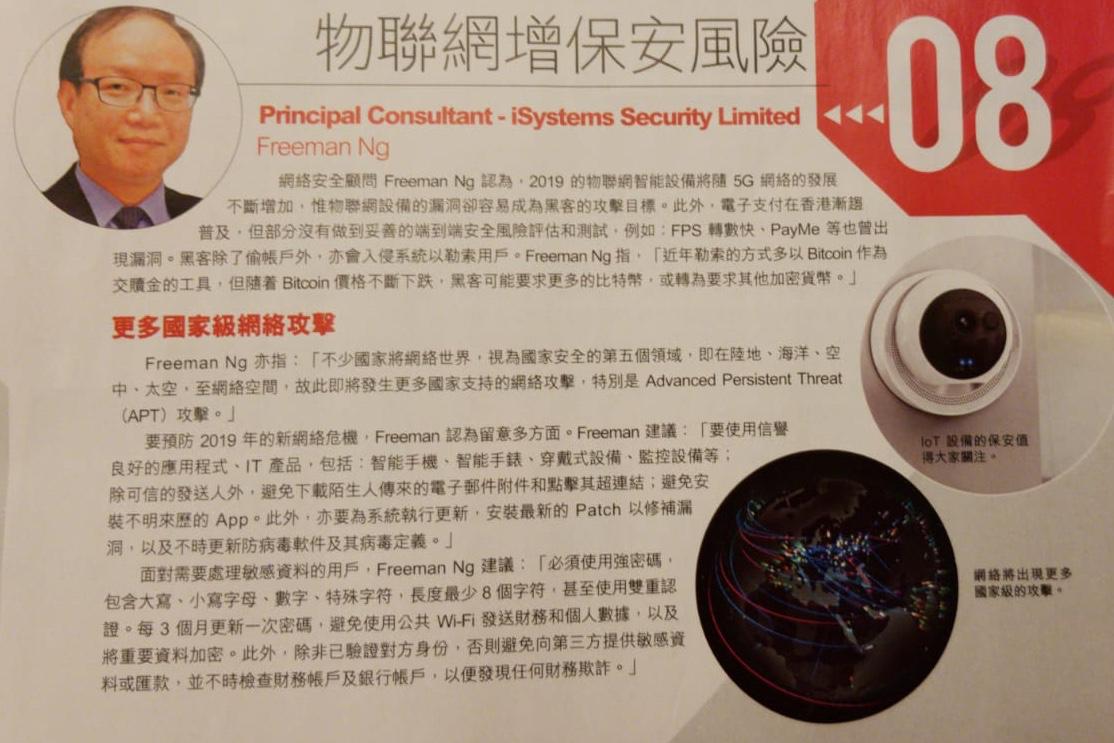
E-ZONE Magazine, Issue 1064, 31/12/2018 Overview
Advanced Persistent Threat (APT) is a kind of cyber attack. From organized cyber criminals to state-sponsored cyber actors, today’s APTs can bypass most security controls and cause serious damages to many organizations. A skilled and determined cyber criminal can use multiple vectors and entry points to navigate around defenses, breach network in minutes and evade detection for months. APTs present a challenge for various organizations. [1]
- Global Positioning System (GPS) is a satellite navigation system used to determine the ground position of an object. GPS technology was first used by the United States military in the 1960s and expanded into civilian use over the next few decades. Today, GPS receivers are included in many commercial products, such as automobiles, smartphones, exercise watches, drones and other GIS devices.