We are proud to announce that iSystems Security has received the certification to ISO 9001:2015 by SGS in recognition of the organization’s Quality Management System, which complies with ISO 9001:2015.
We are delighted to receive the "5 years+ Caring Company" which is accredited by the Hong Kong Council of Social Service since 2017. The Caring Company Scheme aims at building a cohesive society by promoting strategic partnerships among business, public institutions and social service partners; and inspiring corporate social responsibility through develop projects matching with community needs.
It is a honour achieving the Gold Award of Cyber Security Professionals Award 2021! This is a clear recognition of our outstanding performance in the cyber security field
We are pleased on getting the Employer of Choice Award 2021! The Employer of Choice Award, organized by Job Market is a prestigious award for the very best organizations that have demonstrated superior talent management strategies and programs practices. We are proud to receive the Award and we will continue to achieve our effective talent management in the workplace and workforce.
Interview article:
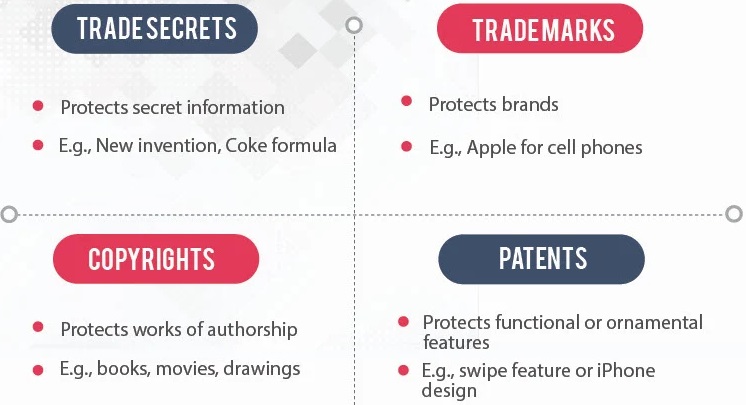
Protecting Intellectual Property: a Cybersecurity Perspective
Intellectual property includes copyrights, trademarks, patents and trade secrets.