Our digital forensic investigators can find the strong evidence behind the mass of scattered and hidden data. With advanced tools, recognized techniques and qualified specialists we analyze your information to provide you with answers to the who, what, and when of investigations and other complex, high-risk situations.
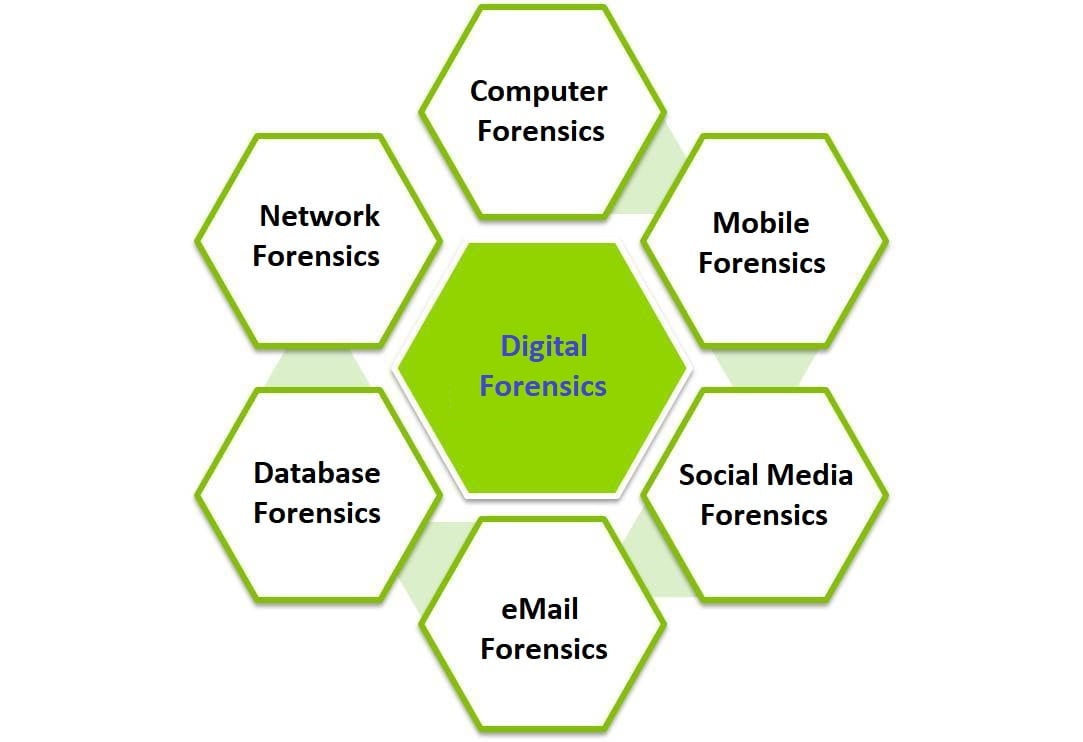 Digital Forensic Services
Digital Forensic Services
- Court-accepted image copies of hard drives and removable media
- Recovery of deleted files
- Analysis of Internet usage
- Analysis of email
- Critical information recovery
- Document and financial data extraction
- Determination of event timelines, e.g. date of document deletion, e-mail, etc.
Our digital forensic specialists are experienced expert witnesses and are able to produce court reports and give evidence in court proceedings, if required.
See our case studies for to find out how Digital Forensics helped with the following cases:
- Defamation and theft of company data
- Confidential data theft
We have helped a wide range of organisations get evidence of illegal and inappropriate use of their company computers. The following scenarios are specific examples of the problems some of our clients have faced in the past. For reasons of client confidentiality and legal sensitivity, actual names have been changed.
Case Study 1: Defame and Fortune
X, the sales manager of Company A gives 4 weeks notice. Soon after he leaves, Company A receives advice from a number of clients that they received emails from an unknown Hotmail account containing defamatory information about Company A.
iSystems Security Ltd is instructed to search for evidence on X's PC that the emails originated from it.
During the briefing iSystems suggests that the PC be examined for any evidence of any confidential data being copied to removable external media during the preceding 4 weeks.
Every bit and byte on the PC's hard disk is acquired and preserved using rigorous procedures. The data is then analysed and various data (deleted) and system files are recovered showing that email data was created at the date and time that X was known to be operating the PC.
Detailed analysis also shows that during the last 3 days of X's employment 1 MYOB data file and 1 Microsoft Access file were copied to a USB drive. The files and detailed report are provided to Company A and appropriate discussions are held with the company's legal advisors for recommended action.
Case Study 2: Competitive Edge
Employee F suddenly resigns from company G and establishes a company in direct competition.
iSystems conducts a detailed briefing session with management and legal counsel of company G. The PC previously used by employee A is studied by iSystems and an evidential copy of all data on the hard disk drive is made and preserved.
The deleted file area undergoes detailed analysis and evidence is found of Company G's confidential marketing data sent as email attachments to a private email account. A deleted draft of a business plan for the new competitive company is also recovered.
A full report is presented to management of company G and the ex-employee F makes appropriate reparation.
